VULNERABILITY ASSESSMENTS AND PENETRATION TESTINGFind Vulnerabilities, Boost Cybersecurity
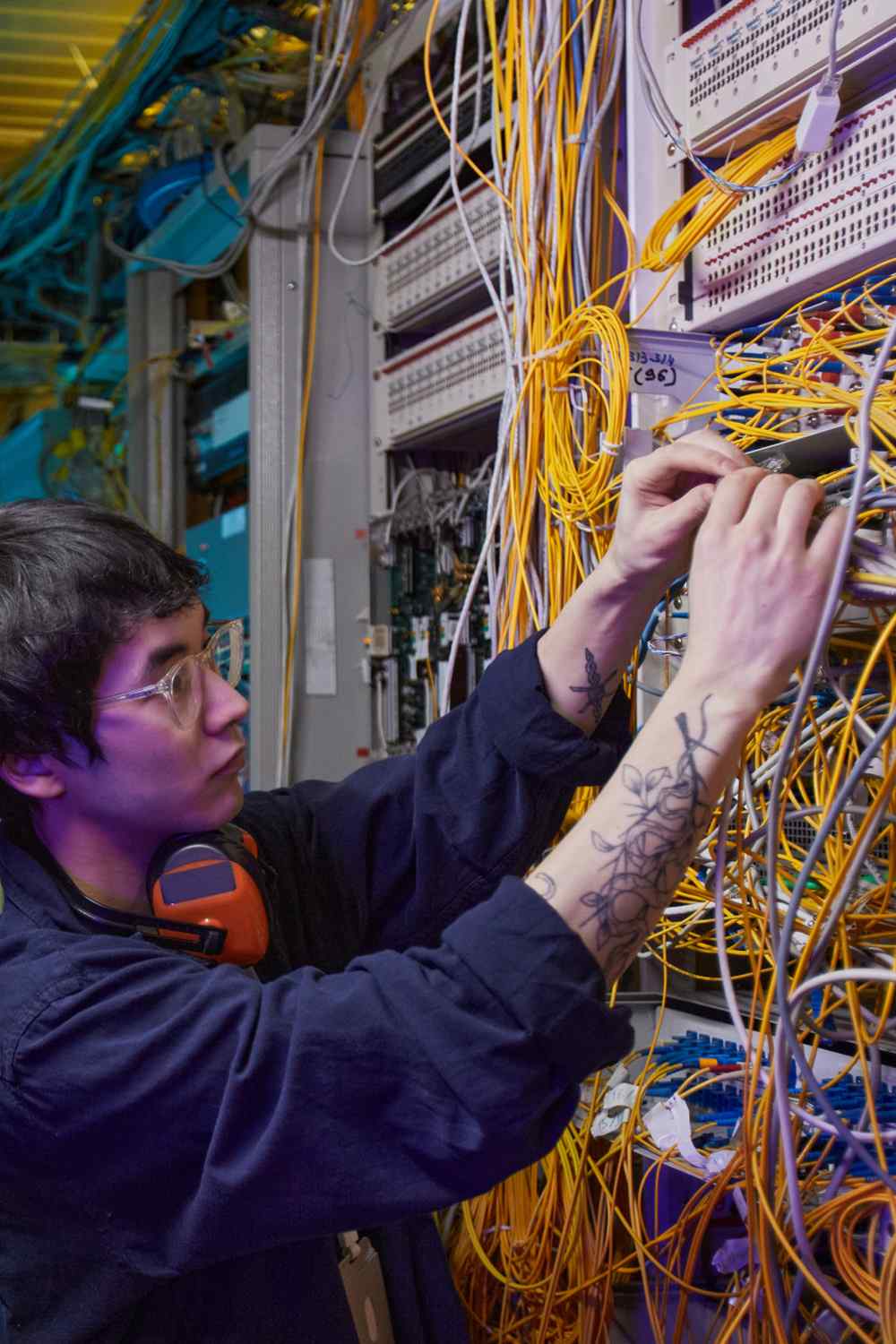
Diagnose Weaknesses, Build Strength
Conduct in-depth scanning across your entire IT infrastructure to identify potential vulnerabilities, utilizing advanced tools and methodologies to uncover hidden risks and weaknesses in your systems.
Strategically develop and implement effective remediation strategies tailored to your specific needs, addressing identified vulnerabilities with precise, actionable solutions to strengthen your cybersecurity infrastructure.
Employ cutting-edge simulation techniques to mimic sophisticated cyber attacks, rigorously testing your defenses under controlled conditions to evaluate the resilience and response capabilities of your security systems.
Ensure the effectiveness of your security measures with regular, thorough assessments, systematically identifying areas for improvement and adapting to the evolving cybersecurity landscape for ongoing enhancement.
of security teams reported encountering zero-day exploits
Our vulnerability assessments and penetration testing services address the challenges of evolving cyber threats by identifying and addressing vulnerabilities in IT infrastructure.
We simulate real-world attacks to accurately uncover weaknesses and provide comprehensive solutions, ensuring your cybersecurity measures are up-to-date and highly effective.
Advance Defense Against Cyber Threats
Conduct a thorough examination of your network to identify potential security gaps and vulnerabilities, utilizing advanced scanning tools to detect and analyze weaknesses that could be exploited by cyber attackers.
Perform rigorous testing of your applications’ security measures against potential breaches, simulating real-world attack scenarios to identify vulnerabilities and strengthen your application defenses effectively.
Critically evaluate the human element of your cybersecurity defenses by testing susceptibility to social engineering tactics, aiming to enhance awareness and preparedness among employees against deceptive cyber threats.
Systematically assess and fortify your wireless networks against unauthorized access, identifying vulnerabilities in your Wi-Fi infrastructure and implementing robust security measures to prevent potential breaches.
Test the effectiveness of physical barriers and security protocols in preventing unauthorized IT access, identifying and addressing any weaknesses in physical security that could lead to cybersecurity risks.
Conduct a comprehensive review and enhancement of your existing cybersecurity policies and protocols, ensuring they are up-to-date, compliant with current regulations, and effectively safeguarding your organization’s digital assets.
Exposing Weaknesses, Enhancing Security
Powered some of the world’s premier brands.