IT SECURITY AUDITSEnhanced IT Security Audits
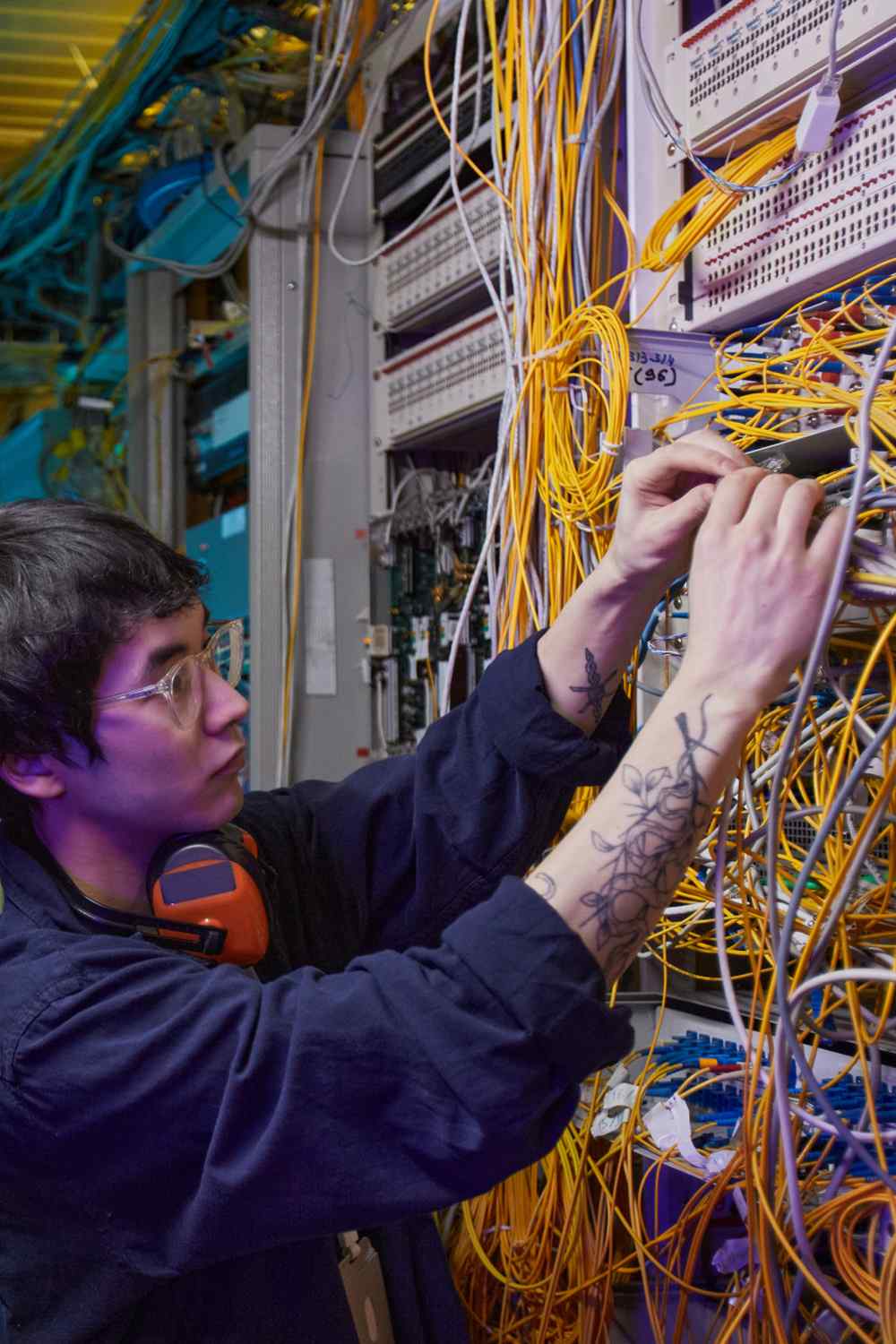
Advanced Security Audits for Proactive Protection
Systematically identify and analyze security weaknesses in your system with our comprehensive vulnerability assessments to fortify your defenses against cyber threats.
Ensure your security measures meet all regulatory requirements for total compliance with our in-depth compliance reviews, keeping your operations aligned with industry standards.
Thoroughly evaluate potential threats and their impact on your operations with our detailed risk analysis, allowing you to prioritize security enhancements effectively.
Develop and implement effective, tailored solutions to address and rectify identified security issues, enhancing your overall security posture and resilience.
human error is responsible for 95 percent of cybersecurity breaches
Our security audits navigate the complexities of cybersecurity and adapt to frequent threat changes, providing clear insights and up-to-date protection.
They effectively mitigate the risks of costly data breaches and ensure strict compliance with all relevant industry and legal cybersecurity standards.
Guardians of Digital Security through Auditing
Perform comprehensive, detailed scans to unearth even the most hidden vulnerabilities in your network, ensuring thorough detection, assessment, and documentation of potential security flaws for proactive defense.
Systematically and rigorously evaluate your existing policies and procedures against current industry best practices and strict compliance standards to ensure your cybersecurity measures are not only up-to-date but also strategically effective.
Carefully and meticulously assess user access controls to guarantee that only authorized personnel have access to sensitive data, thereby safeguarding against unauthorized access and mitigating the risk of potential data breaches.
Thoroughly examine the strength and effectiveness of your data encryption practices, ensuring that your encryption techniques are advanced and robust enough to protect sensitive data from emerging cyber threats and vulnerabilities.
Critically analyze the readiness and effectiveness of your incident response strategies to ensure a rapid, efficient, and coordinated response to cyber incidents, thus minimizing potential damage, downtime, and recovery time.
Diligently and comprehensively scrutinize your network architecture to identify potential security gaps and recommend strategic fortifications, ensuring a resilient and securely fortified network infrastructure against diverse cyber threats.
Protection with Proactive Security Audits
Powered some of the world’s premier brands.